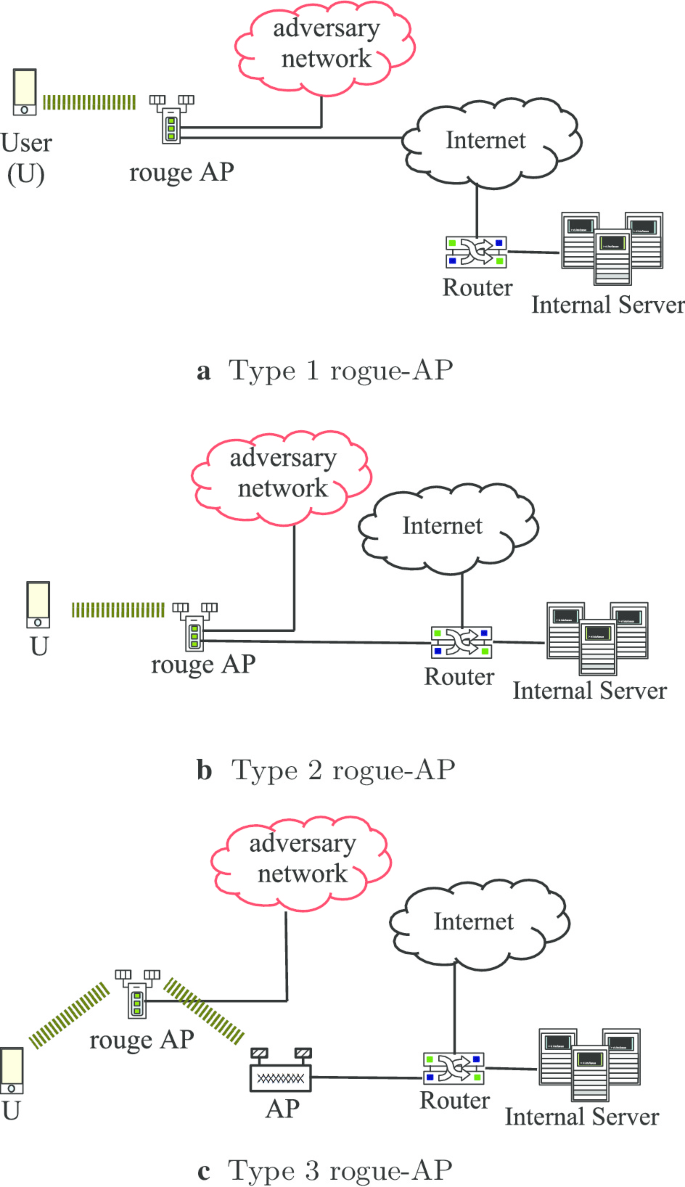
Client-side rogue access-point detection using a simple walking strategy and round-trip time analysis | EURASIP Journal on Wireless Communications and Networking | Full Text

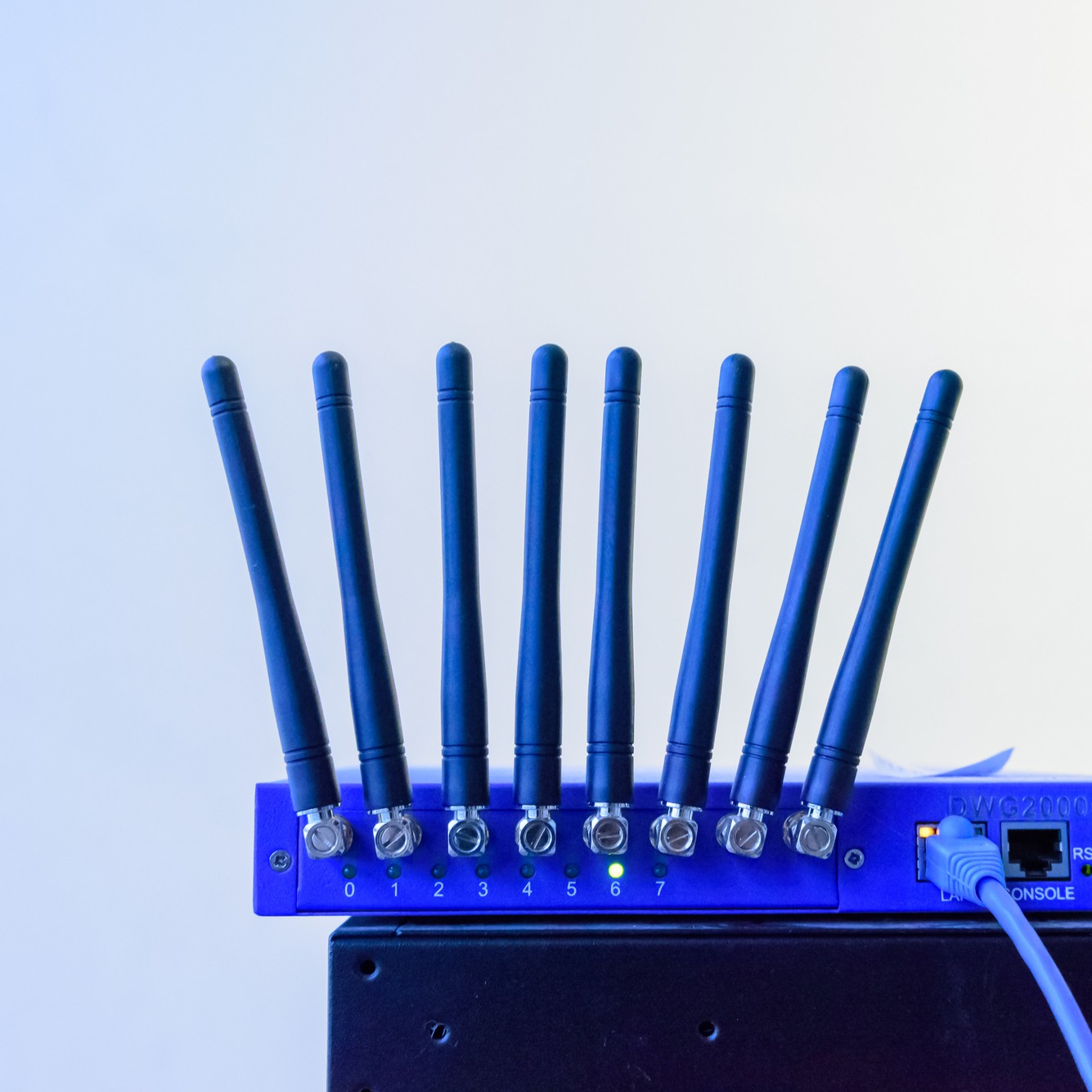
Wireless Access Point Protection: 5 Steps to Find Rogue Wi-Fi Networks and Comply with PCI DSS Requirement 11.1
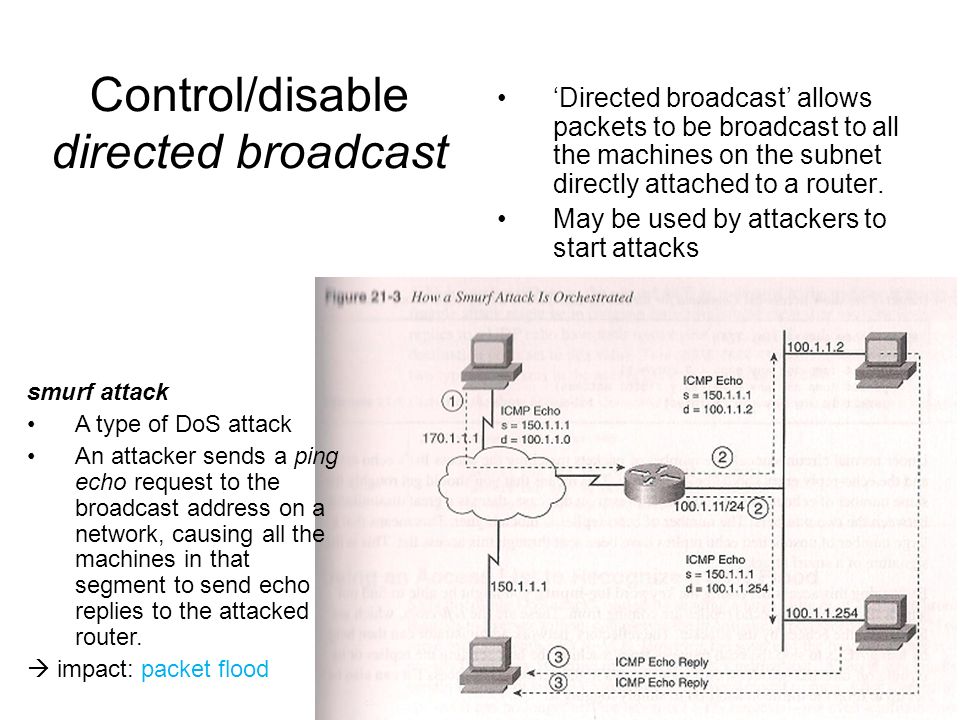
Network Security1 Secure Routing Source: Ch. 4 of Malik. Network Security Principles and Practices (CCIE Professional Development). Pearson Education. - ppt download
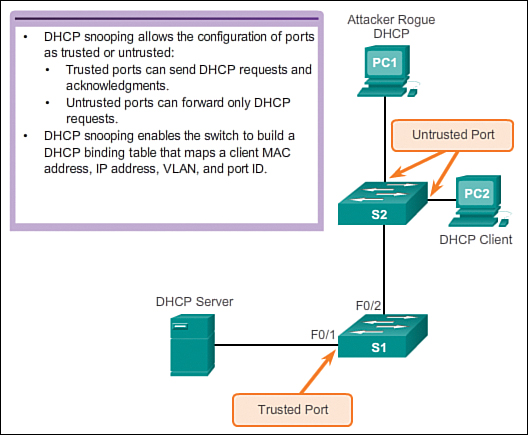
Switch Security: Management and Implementation (2.2) > Cisco Networking Academy's Introduction to Basic Switching Concepts and Configuration | Cisco Press




.png)